Connection
To query your Elasticsearch cluster, you must create a connection.
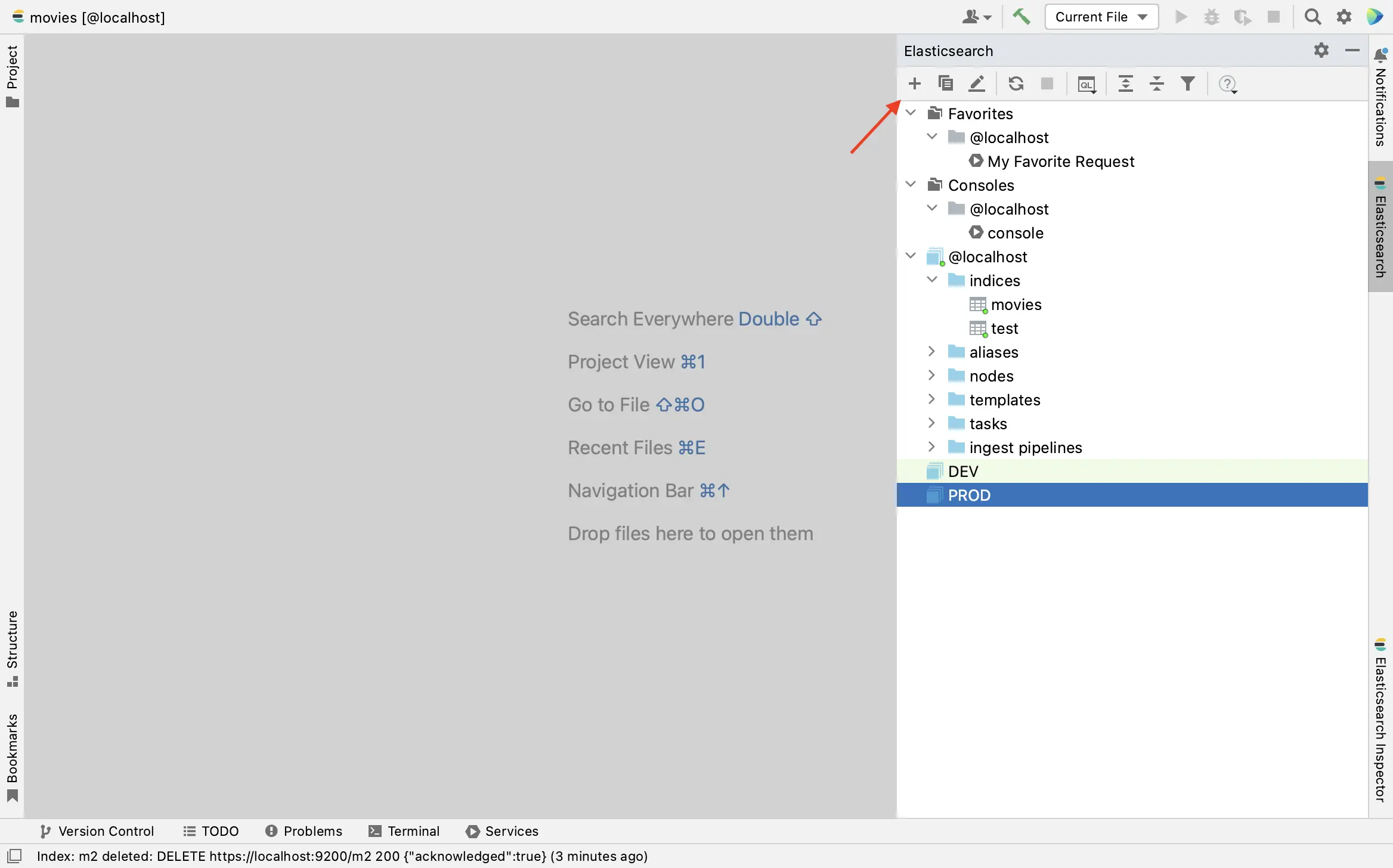
Click + button to open add Elasticsearch cluster dialog:
General settings
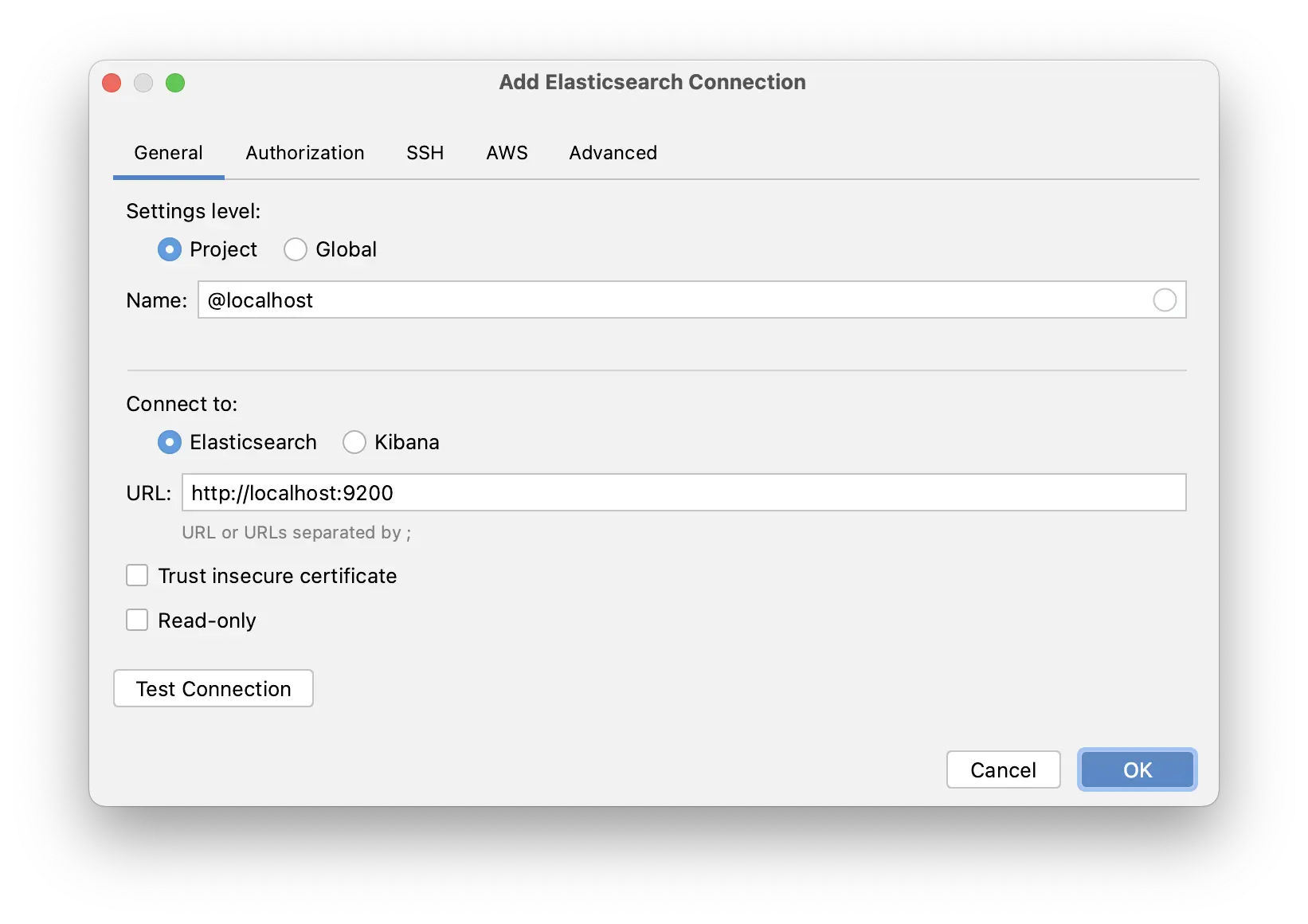
Specify Elasticsearch connection details.
Name field is a label that is associated with this connection.
URL field contains URL or URLs separated by ; of Elasticsearch nodes. HTTP port is required in URL.
If multiple URLs are specified, the HTTP client tries to execute the request for all URLs consequently starting from the last succeed URL until the request succeed or all URLs failed.
Connect to - you can connect to Elasticsearch or Kibana.
Trust insecure certificate - if checked, the HTTP client will trust all certificates, including self-signed certificates.
To ensure that the connection is successful, click the Test Connection button.
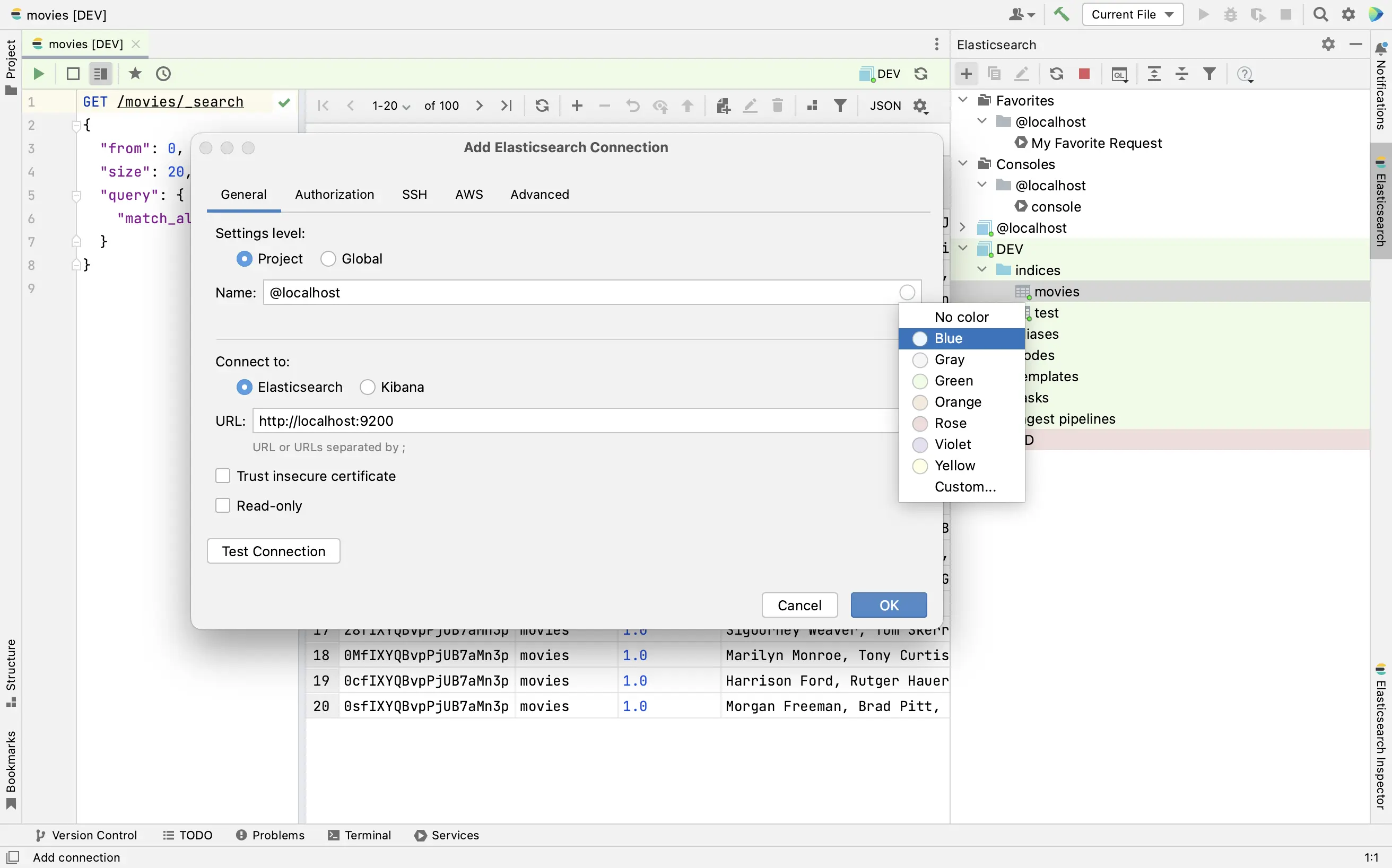
Assign a color to a connection
To have better differentiation between production and test Elasticsearch clusters, you can assign a color to a connection. Click the circle in the Name field to select a color.
Share Elasticsearch connections
The Elasticsearch connections are available at two levels: project and global.
The project level means that you can access Elasticsearch connection only from the project where this connection was created initially.
At the global level, a connection is available for other projects. Also, it can be shared between IDE instances through Settings Sync or Settings Repository
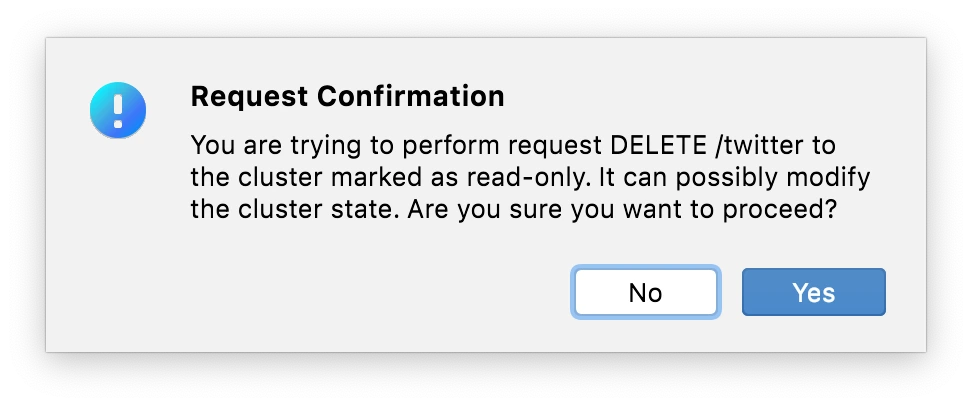
Read-only mode
Read-only checkbox enables Read-only mode for the connection. In Read-only mode all HTTP requests except GET requests require confirmation.
SSL
If your Elasticsearch cluster has enabled TLS/SSL on the HTTP when you try to execute any request the confirmation will be asked:
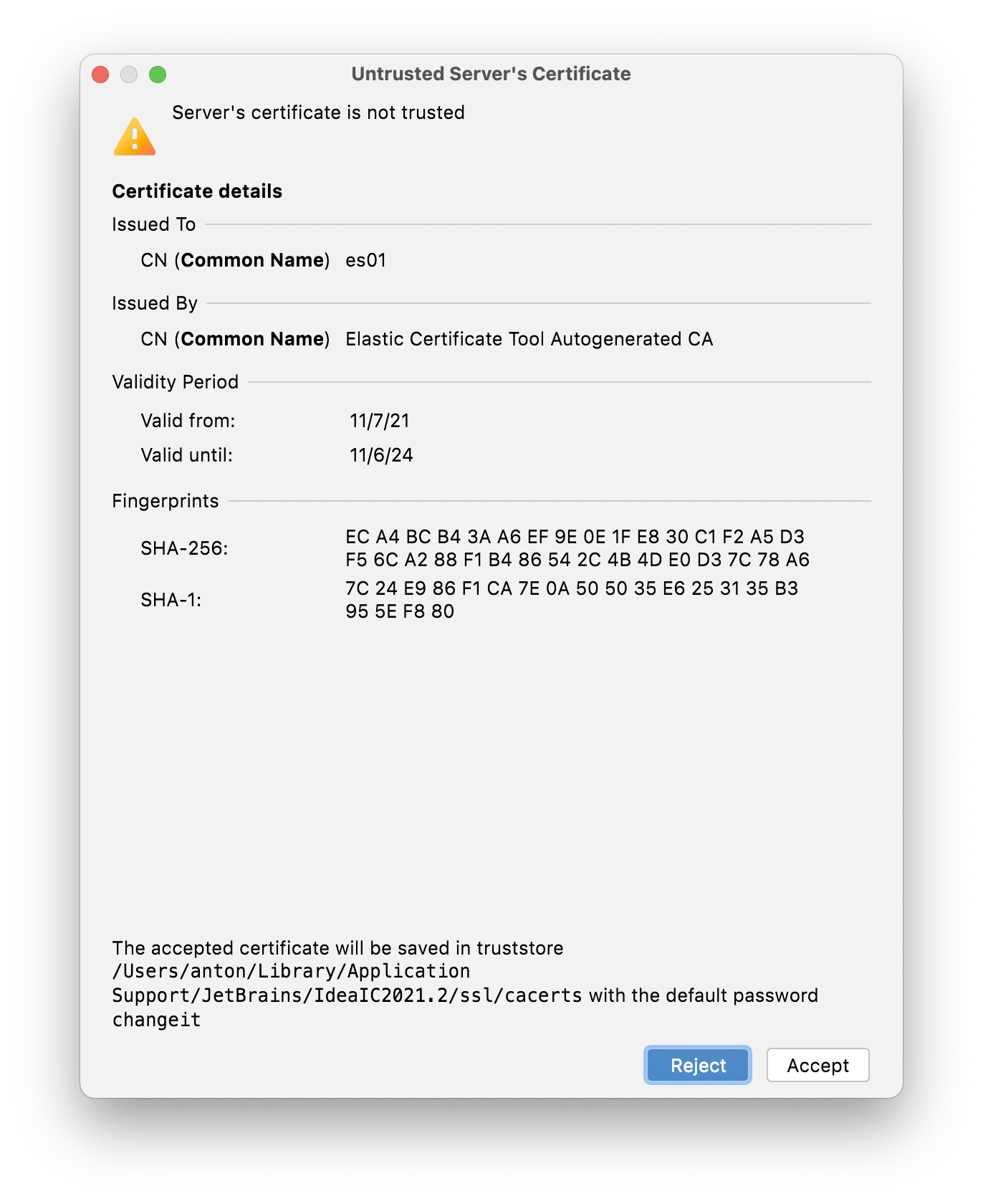 Click the Accept button to trust the certificate. The list of trusted certificates can be found in Preferences | Tools | Server Certificates.
Click the Accept button to trust the certificate. The list of trusted certificates can be found in Preferences | Tools | Server Certificates.
Authorization
Select Authorization tab to configure authorization for the connection. Choose the authorization type and specify credentials. The supported authorization types are: Basic Auth, API Key, Bearer Token and OAuth2.
SSH
Open the SSH tab and select the Use SSH tunnel checkbox.
In Host, User name, and Port fields, specify your connection details.
From the Auth type list, you can select an authentication method:
Password: to access the host with a password.
Key pair (OpenSSH or PuTTY): to use SSH authentication with a key pair. To apply this authentication method, you must have a private key on the client machine and a public key on the remote server. Elasticsearch Plugin supports private keys that are generated with the OpenSSH utility.
Specify the path to the file where your private key is stored and type the passphrase (if any) in the corresponding fields.
OpenSSH config and authentication agent: to use SSH keys that are managed by a credentials helper application (for example, Pageant on Windows or ssh-agent on macOS and Linux).
To ensure that the SSH tunnel is configured successfully, click the Test SSH Connection button.
After you have configured the SSH settings, on the General tab, use the URL of the Elasticsearch node for the remote server. So, if you use SSH tunnel to Elasticsearch node URL should be localhost:{port}.
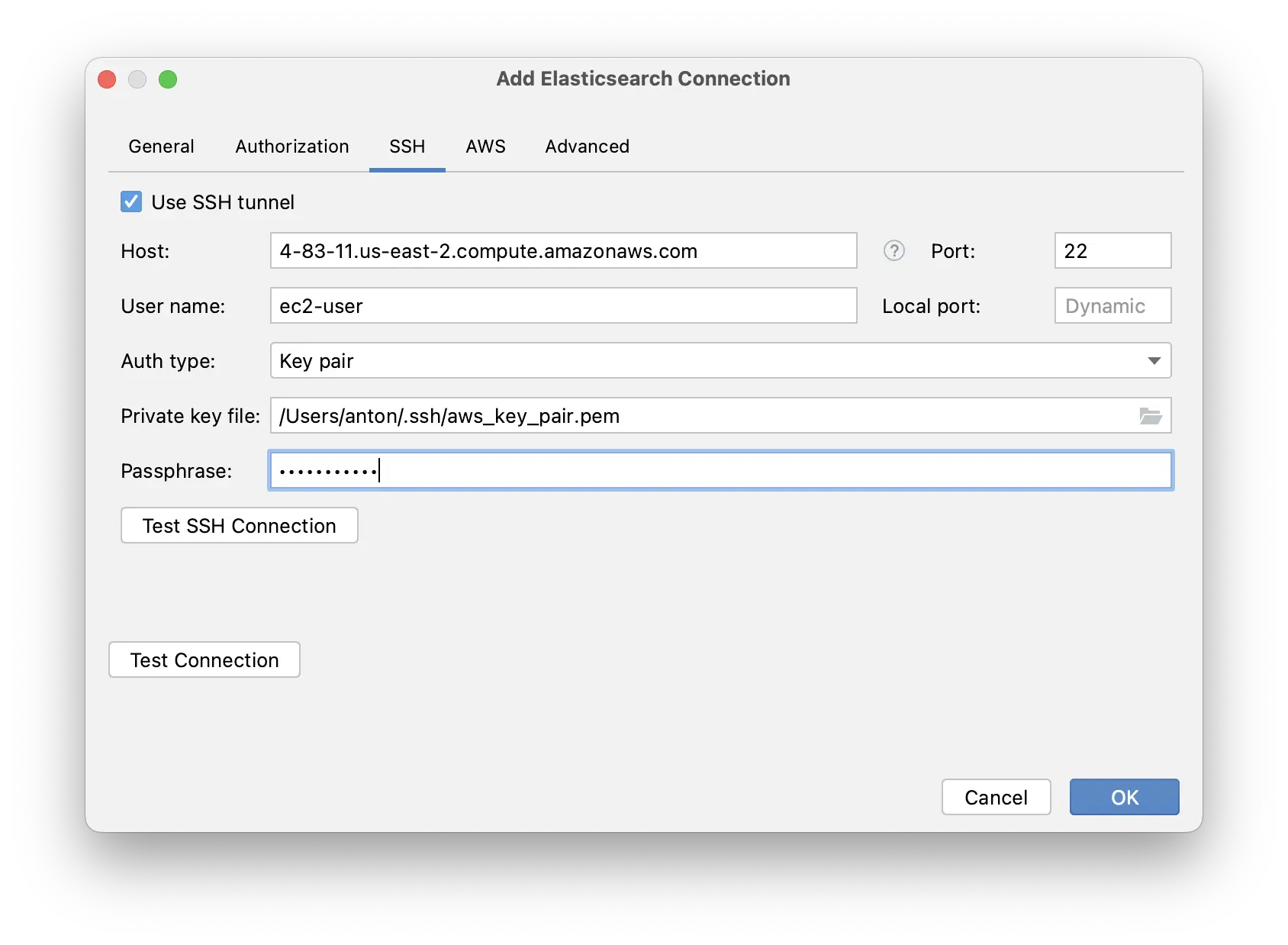
When using jump hosts specify hosts in format [user@]host[:port] separated by comma. For example: ec2-user@bastionHost, ec2-user@remoteHost.
When using OpenSSH config and authentication agent auth type, you can specify HostName, Port, User, ProxyJump in ~/.ssh/config and use host alias.
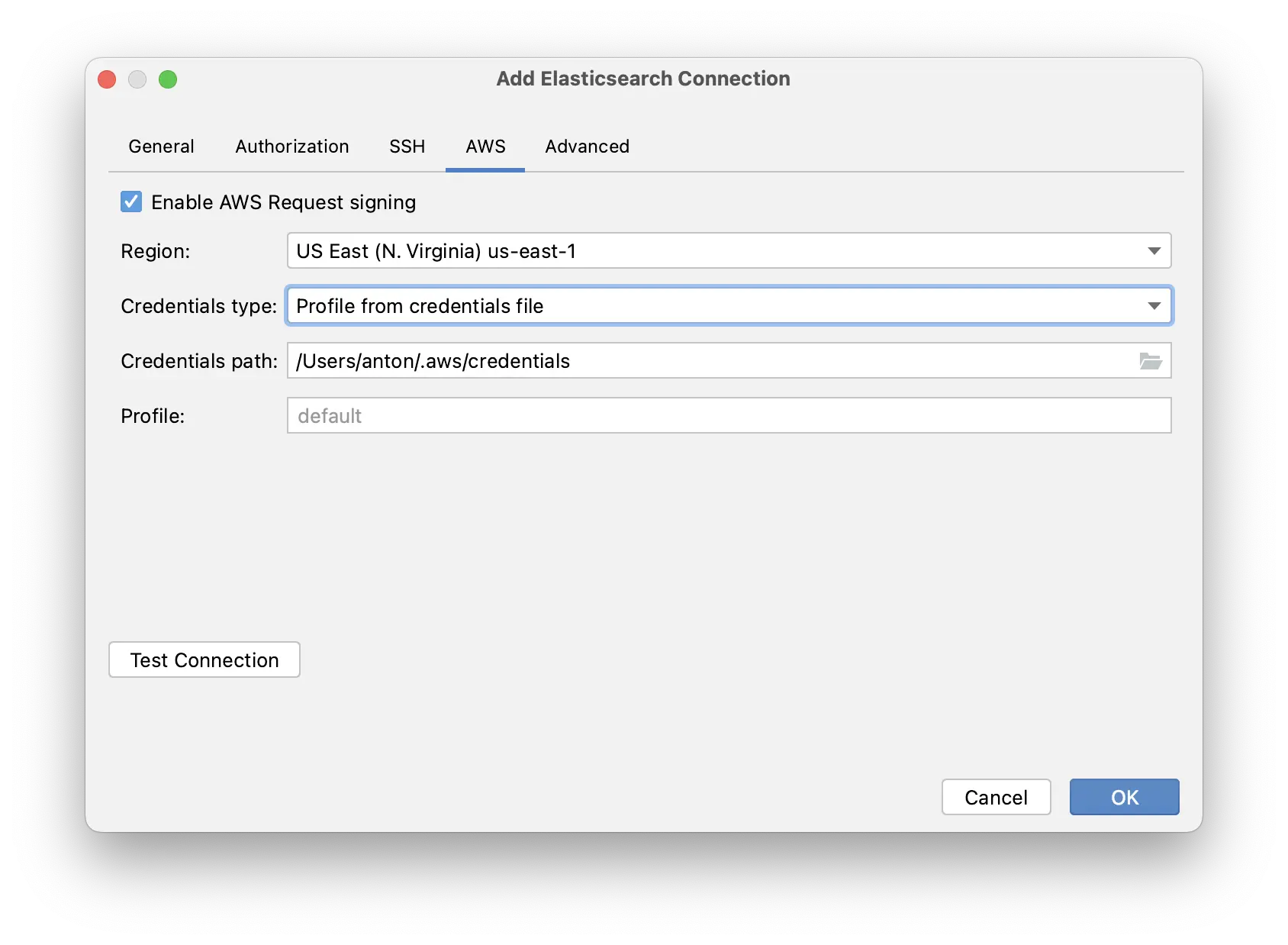
Amazon OpenSearch Service
If you connect to Amazon OpenSearch Service (successor to Amazon Elasticsearch Service)
and your domain access policy includes IAM users or roles (or you use an IAM master user with fine-grained access control),
you must sign requests to the OpenSearch APIs with your IAM credentials.
For signing requests, you need to specify Region and AWS Credentials.
Advanced
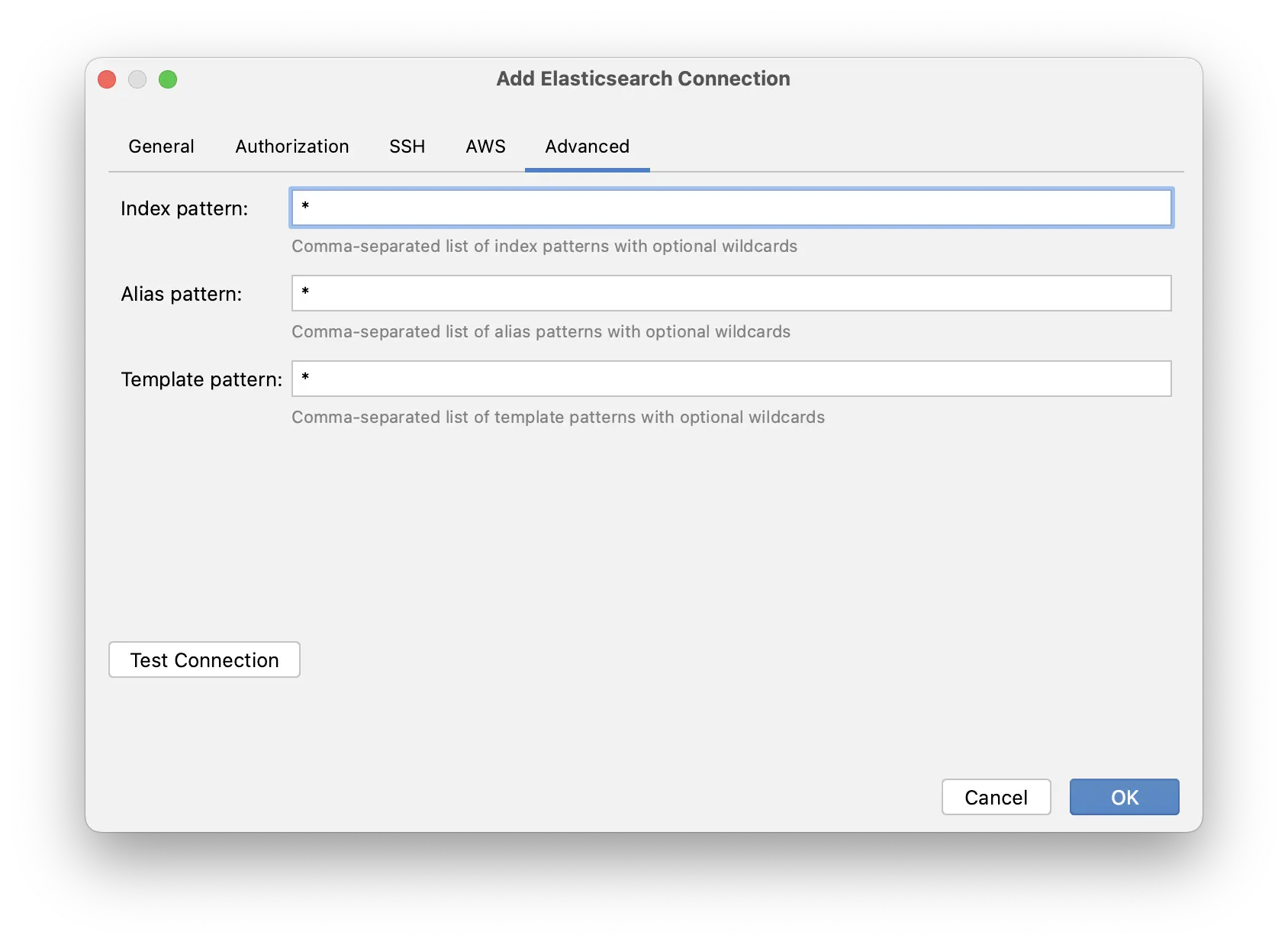
Index Pattern - comma-separated wildcard patterns to filter indices.
Alias Pattern - comma-separated wildcard patterns to filter aliases.
Template Pattern - comma-separated wildcard patterns to filter templates.